1. Introduction: The Parallax Vision
Parallax Network is a decentralized multi-application network engineered to function as a unified hub for digital ownership. The core objective is to bridge the gap between complex cryptographic systems and everyday usability. Parallax empowers users to access decentralized applications (dApps), process transactions, and manage digital assets within a singular, frictionless ecosystem. The guiding principle of the architecture is maximum power through cryptographic abstraction, ensuring the backend handles the complexity while the frontend delivers pure utility.
2. The Structural Problem: The UX Trilemma & The Mobile Bridge
Historically, the evolution of blockchain technology has been plagued by a critical barrier: the friction of user experience (UX). While early blockchains struggled with scalability, modern networks have introduced a new vulnerability: extreme complexity.
The requirement for users to manage non-custodial private keys, comprehend transaction hashes, calculate gas fees, and navigate fragmented security protocols has created a systemic barrier to entry. If interacting with a decentralized ledger requires technical expertise, true mass adoption is mathematically impossible. Parallax operates on the premise that for Web3 to achieve global ubiquity, the underlying blockchain mechanics must become entirely invisible to the end-user.
The Solution: Frictionless Onboarding via "Free Mining"
To dismantle this barrier and drive widespread adoption, Parallax Network introduces a "Free Mining" ecosystem. Instead of requiring users to purchase tokens or configure complex hardware, individuals can join the network simply by downloading and interacting with the Parallax mobile application.
While mobile users do not expend computational power (CPU/GPU hashing), they are a structural necessity for the blockchain's architecture. By interacting with the app, mobile users generate vital static data that builds their Trust Score. This Trust Score serves as the cryptographic routing mechanism for the network: it determines how validation workloads and block proposals are distributed to the actual Node Validators (users running the core software on desktop machines). In essence, the mobile users build the map of trust, and the desktop nodes execute the computational heavy lifting based on that map.
A Unified, Invisible Web3 Experience
For the everyday user, the Web3 learning curve is completely eradicated. The Parallax application is engineered for pure simplicity. There is no confusion over finding decentralized applications (dApps), no tedious multi-chain or cross-chain integrations, and no need to understand underlying blockchain infrastructure.
Users earn token rewards, which will be fully convertible to mainnet assets, simply through participation. Furthermore, the application is designed with forward compatibility. As the ecosystem matures, the app will seamlessly evolve into a unified, secure digital wallet. It will allow users to store, manage, and spend their tokens in an interface as intuitive as traditional banking apps, completely shielding them from cryptographic friction.
3. Sybil Resistance & Privacy: Biometric Identity Hashing and Liveness Verification
The Parallax Network implements a biometric uniqueness mechanism designed exclusively to prevent multi-account abuse. The system operates in two independent stages:
1. Liveness Verification
A real-time liveness detection process verifies that the user is physically present during enrollment and not presenting:
- photographs
- video recordings
- screen replays
- synthetic media
This step ensures the authenticity of the biometric capture event.
2. Local Facial Feature Vectorization
Following successful liveness verification, the client device performs local facial feature extraction by:
- mapping structural facial landmark points
- calculating proportional geometric relationships
- deriving a numerical facial feature vector
No facial image is stored or transmitted to the network. Only a mathematically derived feature vector is produced.
3. Irreversible Cryptographic Hash Generation
The extracted facial feature vector is immediately converted into an irreversible cryptographic hash. Only this hash is stored by the network. The original biometric data:
- is never transmitted
- is never stored
- cannot be reconstructed from the hash
Because facial geometry contains natural micro-variations even between identical twins, the generated hashes provide high probabilistic uniqueness sufficient for Sybil-resistance purposes per individual. This mechanism therefore functions solely as a uniqueness anchor, not as a biometric identity database.
The Mainnet Migration Mandate
While the exact deployment date for Phase 2 is pending, Fuzzy Biometric Hashing will be officially launched prior to the Mainnet release. This verification is a required uniqueness verification step. Users must complete the biometric hashing process to migrate their mined tokens (Verified Balance) to the mainnet. Accounts that fail to generate a valid human hash will forfeit their right to token migration.
Strict Network Rules: One Human, One Node
The protocol enforces an absolute 1:1 human-to-account ratio. The system is equipped with advanced anti-spoofing mechanisms to detect presentation attacks (such as the use of photographs, digital screens, or 3D masks). Any user caught attempting to bypass the biometric liveness check or register multiple accounts will face a permanent exclusion from migration eligibility and reward distribution.
Biometric Tolerance (The "Fuzzy" Mechanics)
A common concern regarding biometric hashing is the natural physical evolution of the user. The "Fuzzy" architecture of the algorithm is specifically designed to accommodate biometric drift. The mathematical model allows for minor physiological deviations; meaning natural changes like haircuts, weight fluctuations, or aging will still resolve to the identical core cryptographic hash. Users are protected against being locked out due to the natural passage of time. All biometric processing occurs locally on the user's device before hash generation.
Identity Decoupling and Wallet Replacement
In traditional Web3 architectures, the user's identity and reputation are irreversibly bound to their cryptographic keypair. Parallax disrupts this rigid structure by decoupling the Identity Layer from the Custody Layer. The user's Trust Score and mining eligibility are strictly tethered to their Parallax Account (secured via the Email + Biometric Hash verification), while the generated PAX tokens are held in the linked non-custodial Wallet (secured via the Seed Phrase). In the event of a security breach where a user's Seed Phrase is compromised, the attacker only gains access to the current funds, but cannot hijack the user's network identity. The legitimate user simply logs into the Parallax application via their biometric anchor, unlinks the compromised wallet, and binds a newly generated Seed Phrase to their account. This ensures that a user's hard-earned Trust Score and network reputation are permanently protected and fully portable, completely eliminating the "risk of ruin" associated with legacy wallet exploits.
4. Consensus Mechanics: Proof-of-Time (PoT) & Graph of Trust (GoT)
Parallax redefines how network participation is valued. Instead of relying exclusively on capital-intensive Proof-of-Stake (PoS) or energy-intensive Proof-of-Work (PoW), Parallax utilizes a hybrid and behavioral validation approach:
- Proof-of-Time (PoT): Validates the continuous, active presence of a node (user) within the network. Even passive engagement, such as syncing balances, contributes to the temporal validation of the ledger.
- Graph of Trust (GoT): A localized reputation matrix. Users build cryptographic weight not just by holding assets, but through their verifiable, consistent interactions with the network over time.
The Behavioral Metric: Human Imperfection vs. Automation
The 4-hour mining cadence is not arbitrary. It is mathematically designed to act as a behavioral liveness filter. Humans are inherently unpredictable and do not remain active 24 hours a day. While it is theoretically possible to complete six full mining cycles daily, constant and uninterrupted execution of this metric strongly indicates automation.
In this consensus model, accounts exhibiting robotic perfection receive a severe penalty to their Trust Score. Conversely, organic users who perform fewer daily cycles and occasionally miss interactions, yet maintain long-term consistency, are rewarded with a significantly higher Trust Score. Currently, the exact calculation of this score is kept closed-source for now to prevent reverse engineering by script creators but it will have an auditable cryptographic mask during the testnet and mainnet periods.
Workload Allocation for Validator Nodes
The Trust Score is the backbone of the network's validation system. It is crucial to distinguish that Mobile Nodes (app users) are not blockchain validators. The structural validation of the network state occurs on Desktop Nodes (Validator Nodes). These require real computational expenditure, though at magnitudes far lower than traditional protocols.
To optimize this computational output and ensure security, Desktop Nodes utilize the Graph of Trust as a workload routing mechanism. The allocation of work, and consequently the rewards, for a validator node is directly proportional to the density and quality of its local network, which includes invited users and subsequent branches.
In practical terms: the higher the aggregated Trust Score of a validator's base (meaning more "human" and organic interactions within their branch), the greater the volume of validations directed to that specific node. This creates an unbreakable economic incentive for validators to build and maintain strictly human communities, naturally isolating any Sybil attack or bot proliferation.
Sporadic Liveness Checks (The Anti-Delegation Filter)
To further deter the outsourcing of mining operations to human click-farms (Account Delegation), the network enforces Sporadic Cryptographic Liveness Checks strictly within the mining interface. At randomized intervals when a user opens the application to initiate a new 4-hour mining cycle or interact with the rewards ecosystem the application will prompt a real-time facial re-validation.
Crucially, because the Sovereign Wallet Layer remains entirely permissionless, these sporadic checks never interfere with standard asset transfers, wallet recoveries, or dApp interactions; they exclusively gate the emission of new PAX tokens. If the real-time scan fails to mathematically align with the account's original Fuzzy Hash, the mining cycle is rejected. This unpredictable verification destroys the economic viability of delegating validated accounts to third-party operators.
5. Dual-Layer Access: Sovereignty vs. Ecosystem Integrity
The Parallax Network distinguishes between Network Participation (holding/transferring assets) and Network Contribution (mining/earning PAX).
5.1. The Sovereign Wallet Layer (Permissionless)
Parallax remains a true decentralized blockchain. Any user can generate a standard ECDSA (Elliptic Curve Digital Signature Algorithm) keypair and a corresponding Seed Phrase.
- Universal Access: Users can create wallets, receive tokens, and interact with the blockchain without any biometric verification.
- Full Custody: The Seed Phrase remains the ultimate "master key." If a user chooses to manage their keys manually, they have 100% control over their assets, consistent with Web3 core values.
5.2. The Mining Gatekeeper (The Biometric Mandate)
While holding tokens is open to everyone, the generation of new PAX tokens (Mining) is strictly reserved for verified humans.
- Verification-Gated Emission: The mining engine in the Parallax App will only activate for accounts that have successfully generated a Fuzzy Biometric Hash.
- Anti-Dilution: This ensures that the 10 Billion PAX supply is distributed into the hands of unique individuals, preventing "ghost nodes" or bot farms from diluting the value of the community's effort.
- Hybrid Onboarding: For the average user, the Biometric/Email flow handles the key management in the background. For the "Power User," the Seed Phrase can be exported or used for cold-storage recovery.
6. Parallax Consensus Protocol (Proof-of-Trust Validation Model)
1. Overview
The Parallax Network operates under a distributed consensus architecture called Proof-of-Trust (PoT), designed to achieve fast transaction finality, deterministic ordering, and scalable parallel validation without relying on Proof-of-Work or classical stake-weighted leader election.
Instead of global validator competition, the network assigns small trust-weighted validation groups that locally verify transactions before they are packaged and permanently stamped by upgraded Core Nodes.
This architecture separates:
- transaction validation
- transaction ordering
- ledger stamping
into distinct coordinated stages.
2. Network Roles
2.1 Validator Nodes
Validator Nodes are responsible for:
- receiving transactions
- participating in trust-based validation groups
- verifying transaction correctness
- voting on transaction acceptance
Validators do not mine blocks and do not solve cryptographic puzzles. Their influence derives from their accumulated trust score within the network graph.
2.2 Core Nodes
Core Nodes are upgraded Validator Nodes that:
- accumulated high trust reputation
- locked a required collateral amount of PAX tokens
- were promoted automatically by network rules
Core Nodes are responsible for:
- aggregating validated transactions
- assembling transaction batches
- stamping the canonical ledger
Core Nodes do not re-validate transaction logic. They finalize already-validated transaction sets.
3. Trust Graph and Validator Selection
The Parallax Network maintains a dynamic trust graph linking participants through:
- direct referrals
- indirect referral chains
- historical validation accuracy
- behavioral reliability
For each incoming transaction:
- The network selects a validation group of fixed size (fixed committee size: 47 validators).
- Validators are drawn probabilistically.
- Selection probability equals the combined trust weight of candidate clusters.
Thus, validation power emerges from distributed trust density rather than stake concentration. Committee size is intentionally fixed at 47 to balance adversarial resistance, network latency, and validator distribution efficiency under expected network scale.
Validator Group Formation and Rotation
Transactions are validated by dynamically assigned validator committees composed of 47 validator nodes. Validator committees remain active for a fixed operational window of 10 successfully finalized blocks, after which a new committee is selected using the same cryptographic randomness mechanism employed for Core Node batch selection.
Given an average block finalization time of approximately 10 seconds, validator committees rotate roughly every 100 seconds, ensuring continuous reshuffling of trust relationships and minimizing the probability of persistent adversarial coordination.
This rotation mechanism guarantees:
- continuous redistribution of validation responsibility
- prevention of long-term validator capture
- probabilistic fairness in committee assignment
- long-term decentralization of trust influence
4. Transaction Lifecycle
Each transaction passes through five deterministic stages.
Stage 1: Submission
A user submits a transaction containing: sender address, recipient address, value, sequential account nonce, and digital signature.
Stage 2: Sequential Nonce Enforcement
Each account maintains: last_confirmed_nonce. A transaction is considered eligible only if: nonce = last_confirmed_nonce + 1.
Future nonce handling: If nonce > expected_nonce, the transaction enters a temporary sequence buffer. The buffer retention window is strictly bounded. The transaction remains in the buffer for up to 2 block completions (approx. 20 seconds). If the missing preceding nonce does not appear within this interval, the buffered transaction is rejected. This prevents indefinite queue growth while tolerating network propagation disorder.
Stage 3: Account Pending Lock
Once a transaction with the correct next nonce enters validation: account_pending_lock = TRUE. While locked: additional future transactions may be received, but only the lowest nonce transaction may enter validation consensus. This guarantees strict chronological execution per account. This mechanism prevents: double spending attempts, parallel conflicting validations, and cross-group sequence violations.
Stage 4: Local Trust-Weighted Group Validation
Upon passing sequential eligibility checks, the transaction is assigned to a randomly selected validator group derived from the network trust graph.
Example structure:
- total validators: 500
- group size: 47
Excess users who were not drawn in a group are excluded from validations and await the next rotation of validators after 10 blocks.
The assigned group independently verifies:
- signature authenticity
- balance sufficiency
- nonce correctness
- protocol rule compliance
Each validator broadcasts a signed approval or rejection vote.
Validation Time Window
Each validator committee is given a target validation window of approximately 3 seconds, dynamically adjustable by protocol parameters according to observed network latency, to submit signed approval or rejection votes for a transaction. Votes received after this window are discarded and do not contribute to the consensus decision. This bounded validation interval ensures deterministic latency guarantees and prevents indefinite transaction stalling.
Partial Validator Response Handling
If more than 30% of validators fail to respond before timeout expiration (15 or more), the transaction is automatically marked as: the validation timeout has expired, and the validation has been allocated to another group. The user may resubmit the transaction afterward using the same sequential nonce value. This rule prevents validation deadlock while maintaining strict responsiveness guarantees across the network.
A transaction is considered locally finalized once a strict simple majority of validators within the assigned group approve it:
approved_votes > group_size / 2
The majority threshold is always calculated against the full committee size, not against the number of received votes. This majority-based validation implements a localized Byzantine fault-tolerant agreement model executed within dynamically selected validator committees.
Instead, security derives from three combined mechanisms:
- randomized validator assignment per transaction
- trust-weighted selection derived from long-term behavioral reliability
- cryptographic vote signing and public verification
Because validator groups are: independently selected, probabilistically trust-distributed, and continuously reshuffled per transaction, the probability of coordinated malicious majority capture becomes statistically negligible under normal network trust distribution. This model therefore provides: probabilistic adversarial resistance through randomized trust-weighted local consensus, rather than classical deterministic Byzantine Fault Tolerance guarantees.
Because groups are small and validation is localized:
- consensus latency remains extremely low
- network throughput scales horizontally
- multiple validator groups may process independent transactions simultaneously
Stage 5: Ledger Stamping by Core Nodes
Approved transactions are not immediately written to the global ledger. Instead: validated transactions enter the global validated pool, Core Nodes aggregate them into ordered batches, and batches are stamped onto the canonical ledger. Stamping establishes: permanent ordering, global finality, and state transition.
6.1 Verifiable Random Core Node Selection
To guarantee neutrality, unpredictability, and resistance to manipulation, the Parallax Network employs a Verifiable Random Selection mechanism for choosing the Core Node responsible for assembling and stamping each ledger batch.
This mechanism combines:
- a distributed entropy pool generated collectively by active validators
- a cryptographic Verifiable Random Function (VRF) executed independently by each eligible Core Node
This hybrid approach ensures that batch assembly authority cannot be predicted, influenced, or monopolized.
6.1.1 Distributed Entropy Generation
At regular protocol intervals, the network generates a fresh epoch seed through a commit-reveal entropy process. During this process: Active validator nodes locally generate a random value. Each validator first broadcasts the cryptographic hash of its value (commit phase). After the commit window closes, validators reveal the original values (reveal phase). The protocol aggregates all revealed values and computes: epoch_seed = HASH(all_revealed_values).
Because no participant can predict the combined output in advance, the resulting seed becomes a collectively generated unpredictable randomness source. Validators that fail to reveal their committed value within the allowed window are excluded from the entropy round and may incur trust penalties.
6.1.2 Verifiable Random Function Execution
Once the epoch seed is finalized, every eligible Core Node independently computes: vrf_output = VRF(core_private_key, epoch_seed).
The VRF produces: a pseudo-random numerical output and a cryptographic proof allowing any network participant to verify correctness. This guarantees that the result: cannot be fabricated, cannot be modified after generation, and remains publicly verifiable without revealing the node's private key.
6.1.3 Core Node Selection Rule
After all VRF outputs are broadcast: the network compares the numerical VRF outputs, the Core Node with the lowest valid output is deterministically selected, and ties are resolved using deterministic address ordering. Because every Core Node uses the same unpredictable seed, and because VRF outputs are provably authentic, the selection process remains: fully decentralized, unpredictable prior to execution, and immune to manual manipulation. All eligible Core Nodes participate with equal weight in this selection process. Trust score does not influence Core Node lottery probability.
6.1.4 Security Guarantees
- Unpredictability: No node can know the selection outcome before the entropy reveal phase completes.
- Manipulation resistance: No single participant controls the seed generation.
- Public verifiability: All VRF outputs and entropy inputs can be independently validated.
- Equal opportunity selection: All Core Nodes share identical selection probability.
6.1.5 Consensus Design Rationale
The Parallax Network intentionally separates: transaction validation authority (Validator Nodes) and ledger organization authority (Core Nodes). Because transactions are already finalized prior to stamping, the Core Node selection mechanism does not determine transaction validity, but strictly determines ledger assembly responsibility. This design allows the network to maintain deterministic transaction finality while still preserving decentralized and unpredictable ledger organization.
6.2 Core Node Batch Stamping and Finalization
Deterministic Transaction Finality
In the Parallax Network, transaction finality does NOT occur at the ledger stamping stage. A transaction is considered FINAL once:
- it has been validated by its assigned validator group
- the majority Byzantine threshold (>50%) has been reached
- the signed validation result has been broadcast to the network
A transaction reaches consensus finality after validator approval and becomes permanently recorded once stamped into the canonical ledger. Core Nodes do not participate in transaction decision logic and cannot overturn validated results. Their role is strictly organizational.
Separation Between Validation and Ledger Organization
The Parallax architecture explicitly separates: Transaction validation (performed by Validator Nodes) and Ledger organization and stamping (performed by Core Nodes).
- Validator Nodes: verify signatures, verify balances, verify nonce ordering, vote on acceptance.
- Core Nodes: collect already-validated transactions, assemble ordered batches, stamp the canonical blockchain. Core Nodes never independently approve or reject transactions.
Random Core Node Selection
To assemble each ledger batch, the network performs a uniform random selection among all eligible Core Nodes. Rules: every Core Node has equal probability, no trust weight advantage exists at this stage, selection is fully protocol-driven, manual selection is impossible. This guarantees that ledger stamping power cannot accumulate through trust concentration or capital dominance.
Single Active Batch Rule
The network enforces a single active stamping process at any given moment. Once a Core Node is selected: it becomes the temporary batch assembler, no other Core Node may stamp concurrently, and competing batch creation attempts are ignored. This prevents ledger branching and eliminates competing canonical histories. Because transactions are already finalized prior to stamping, parallel stamping provides no security advantage and is intentionally disallowed. The validated transaction pool remains globally preserved and unaffected during Core Node reselection.
Batch Assembly Process
The selected Core Node: pulls validated transactions from the global validated pool, sorts them deterministically, assembles them into a batch, computes the batch hash, appends the batch to the blockchain. The batch acts purely as a historical ordering container.
Failure Handling
If the selected Core Node: goes offline, fails to assemble a batch within the allowed window, broadcasts an invalid batch structure, the network automatically triggers a new random Core Node selection. Previously validated transactions remain valid and unaffected.
Consensus Philosophy of Core Nodes
Core Nodes are intentionally designed to function as: deterministic ledger organizers, not consensus authorities. Security derives from distributed validator agreement, not from block producers. This architecture removes: mining races, leader dominance, fork competition, probabilistic settlement, and replaces them with: validator-driven deterministic finality and randomized organizational stamping.
6.3 Parallelism Model
The Parallax Network supports safe parallel validation under one constraint: A single account cannot have multiple active consensus-eligible transactions simultaneously. However: different accounts may validate transactions concurrently, multiple validator groups may operate in parallel, multiple transaction batches may be processed simultaneously. This achieves high throughput without violating chronological account execution.
6.4 Transaction Expiration Rules
Transactions waiting for missing nonce predecessors: remain buffered only within the bounded wait window and expire automatically if sequence completion fails. This prevents: mempool inflation attacks, intentional sequence blocking, and propagation manipulation.
6.5 Security Properties
The Proof-of-Trust model guarantees:
- Deterministic account ordering: Every account executes transactions strictly sequentially.
- Adversarial resistance: Randomized trust-weighted validator grouping combined with signed majority voting provides probabilistic protection against coordinated malicious participation.
- Sybil resistance via trust graph density: Validator influence requires long-term network participation rather than instantaneous stake injection.
- Fast finality: Small group validation drastically reduces consensus latency.
- Horizontal scalability: Parallel independent validation groups allow throughput growth with validator expansion.
6.6 Promotion Mechanism for Core Nodes
A Validator Node becomes eligible for Core status when: its trust score exceeds the network limit, its historical validation reliability remains above the minimum, and a significant amount of PAX collateral is locked. Users can apply to become core nodes and operate as validator nodes until they meet the minimum conditions, the promotion is automatic and rule-based. Core Nodes that behave maliciously risk: collateral slashing, trust reset, automatic demotion.
6.7 Consensus Philosophy
The Parallax Consensus design is based on three principles: Trust accumulation replaces computational waste, local validation replaces global contention, deterministic sequencing replaces probabilistic ordering. This allows the network to achieve: low latency, high throughput, strong consistency, sustainable validator participation without mining or classical stake races.
7. Network Architecture & Incentives: The Tri-Layered Model
Traditional blockchains often trend toward centralization through massive validator pools or suffer from severe bottlenecks by forcing every node to validate every transaction. Parallax introduces a Tri-Layered Node Architecture to enforce decentralization by design, segmenting workloads and economic rewards based on trust and processing capacity.
The Three Tiers of the Parallax Network
The ecosystem is divided into three distinct functional layers, each playing a critical role in the consensus process and featuring its own distinct reward mechanism:
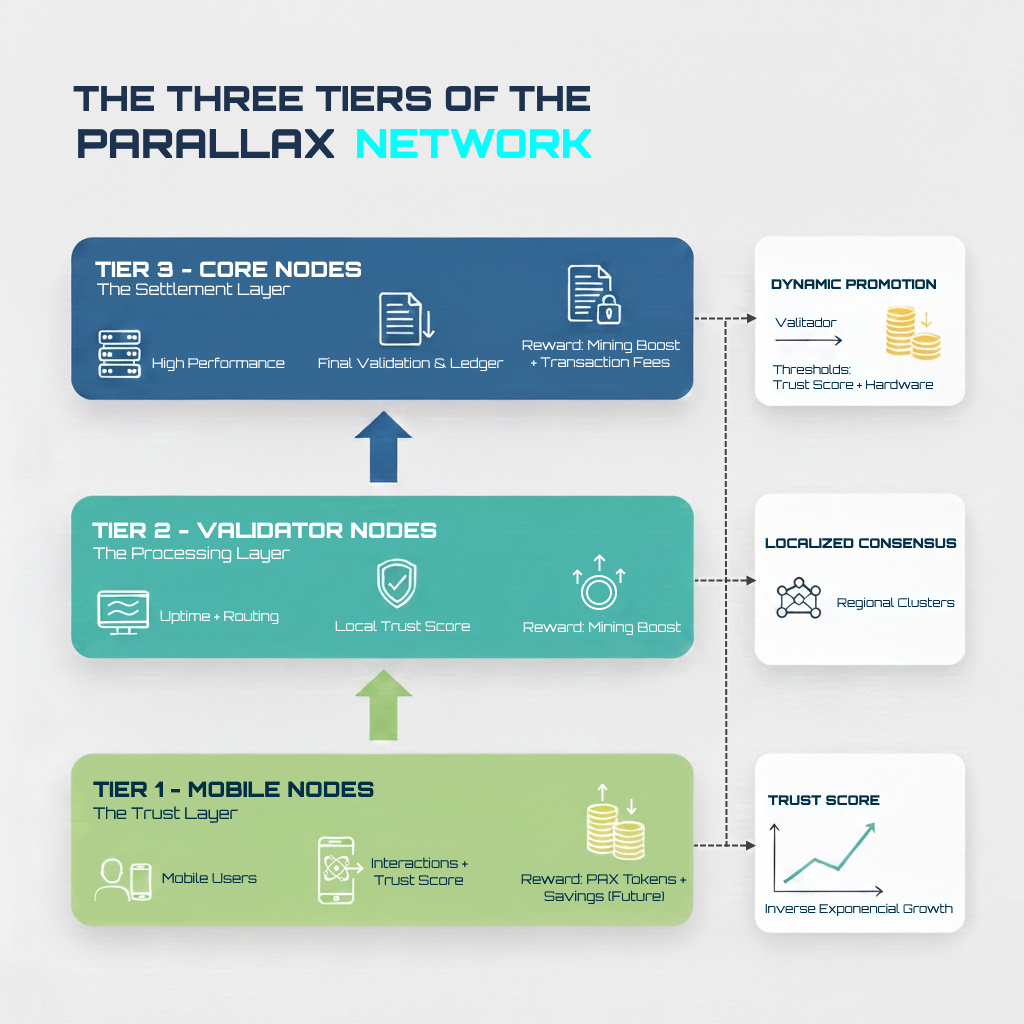
- Tier 1: Mobile Nodes (The Trust Layer)
These are the everyday users interacting via the mobile application. While they do not perform heavy computational hashing, they are the foundational layer of the network. Through their organic interactions, they generate the static data known as the Trust Score, actively building the localized Graph of Trust.
Reward Mechanism: Mobile Nodes earn PAX tokens proportionally to their active participation in mining cycles. In future protocol upgrades, the Savings Protocol will be integrated; meaning users who hold and store their tokens will receive a mathematical multiplier on their baseline interaction yields. - Tier 2: Validator Nodes (The Processing Layer)
Operated by users running the core software on standard desktop machines. Validator Nodes handle the bulk of localized, lightweight network traffic and data packet routing.
Reward Mechanism: Instead of traditional block rewards, Validator Nodes receive a dynamic multiplier (Mining Boost) applied to their base mining cycles. The magnitude of this boost is directly proportional to their verifiable network uptime and the aggregated Trust Score of their surrounding node branch. - Tier 3: Core Nodes (The Settlement Layer)
Advanced desktop nodes with higher processing capabilities. Core Nodes manage the heaviest computational tasks, acting as the final cryptographic authority for organizing and stamping state updates onto the global ledger.
Reward Mechanism: Core Nodes receive the highest tier of economic incentives. In addition to maximizing their Mining Boost, these nodes earn a direct percentage of the transaction fees generated by the network traffic they successfully process and settle.
Localized Consensus and Dynamic Promotion
Transactions within the Parallax Network are not broadcasted to the entire global ledger simultaneously. Instead, they are fragmented into smaller data packets validated by a specific subset of surrounding Validator Nodes.
Parallax is designed to scale organically. A Validator Node is not permanently restricted to Tier 2. If a Validator Node meets specific hardware processing requirements and accumulates a critical mass of Trust Score from its surrounding network, it automatically becomes eligible for promotion to a Core Node.
The Inverse Exponential Trust Curve
To prevent any single node or cluster from monopolizing network consensus, the accumulation of trust is mathematically capped. The Trust Score follows an inverse exponential growth curve. In practical terms: the more Trust Score a node possesses, the exponentially harder it becomes to acquire more.
This mathematical friction ensures that power cannot be endlessly centralized by a few early or massive nodes. Furthermore, when a specific region of the Trust Graph becomes too dense, the protocol automatically elects a highly trusted Validator Node in that sector to become a new Core Node, perpetually distributing validation power and rewards toward the edges of the network.
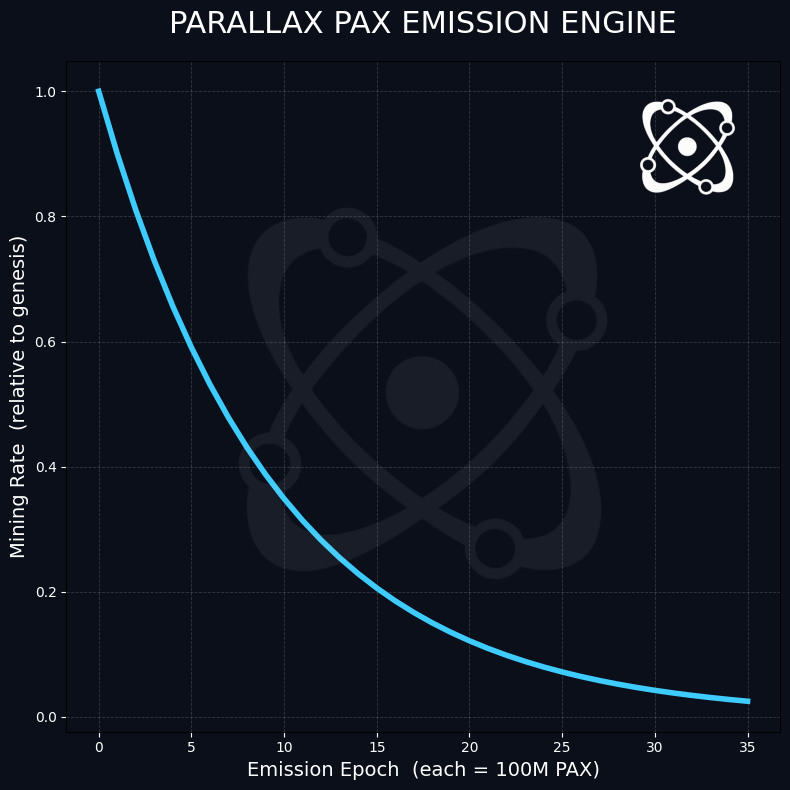
8. Economic Model: The Deflationary Epoch Engine
The Parallax economic engine is designed to ensure long-term scarcity and reward early network bootstrapping. The native utility token, PAX, has a hard-capped maximum supply of 10,000,000,000 (10 Billion) tokens. It is crucial to note that this maximum cap is a mathematical ceiling, not a target metric. The actual circulating supply is governed by strict deflationary mechanisms and user behavior.
Unlike time-based emission schedules, which are vulnerable to fluctuating network activity and can over-inflate supply during low-usage periods, Parallax utilizes a dynamic Emission Epoch Protocol triggered strictly by total network output.
The Halving Algorithm and Emission Formula
The base mining rate is algorithmically reduced by 10% for every 100,000,000 (100 Million) verified PAX emitted. The network emission rate follows a specific decay function:
Rn = R0 × (0.90)n
Where Rn is the new rate, R0 is the genesis rate, and n is the current Epoch (increments of 100M PAX). This ensures that as the network matures, token generation becomes mathematically harder, creating natural scarcity.
Yield Generation: The Mining Calculation
The individual user yield is not a static number. It is a composite calculation that rewards consistency and network expansion. A standard mining cycle lasts exactly 4 hours. The total PAX generated per cycle is calculated through the following components:
- Base Yield: The current active Epoch Rate (PAX/h) multiplied by 4.
- Daily Streak Multiplier: A compounding boost awarded for consecutive daily check-ins.
- Network Expansion Bonus: Additional yield based on the active participation of invited users.
- Node Infrastructure Boost: In future phases, users operating Desktop Validator Nodes will receive significant multipliers on top of their base cycles as compensation for their hardware output.
- The Savings Protocol Boost: Post-Mainnet, Parallax will introduce a frictionless alternative to traditional staking. Users who allocate their balance to the Savings Protocol will receive a proportional multiplier on their ongoing mining cycles, economically rewarding long-term holders without the complexity of smart-contract lockups.
Mainnet Migration and The Token Generation Event (TGE)
Not all tokens generated within the mobile application will enter the live blockchain immediately. To protect the network from instant hyper-inflation and dump mechanics, migrated tokens will be subject to a Trust-Weighted Vesting Schedule. During the Mainnet TGE, tokens are released linearly over a specified number of months based on a precise matrix comparing the user's Total Balance against their Graph of Trust (Trust Score):
- Low Balance + High Trust Score: Immediate or near-immediate unlock of the full balance.
- Low Balance + Low Trust Score: Intermediate vesting period.
- High Balance + High Trust Score: Intermediate vesting period, rewarding large holders while protecting market liquidity.
- High Balance + Low Trust Score: The maximum vesting duration. This severely restricts potential bad actors who accumulated large balances without organic, trusted network behavior.
Initial Circulating Supply Dynamics
The transition to Mainnet acts as a massive deflationary filter. A significant portion of the currently mined tokens will never reach the live blockchain due to natural user abandonment, lost accounts, or permanent bans resulting from Sybil attacks (multi-accounting and botting detected by the Fuzzy Biometric Hash).
Coupled with the Trust-Weighted Vesting Schedule, the initial liquidity pool will be highly restricted. Based on network projections, the circulating supply at Mainnet launch is estimated to be approximately 100,000,000 (100 Million) PAX. This low initial supply, paired with high utility demand, establishes a robust economic foundation for the Parallax ecosystem.
9. Token Allocation & The Community-Pegged Vesting Protocol
To ensure absolute alignment between the protocol creators and the network participants, Parallax Network employs a transparent, anti-dilutive token distribution model. The hard-capped maximum supply of 10,000,000,000 (10 Billion) PAX is rigidly partitioned to prioritize the users:
The 90/10 Macro Allocation
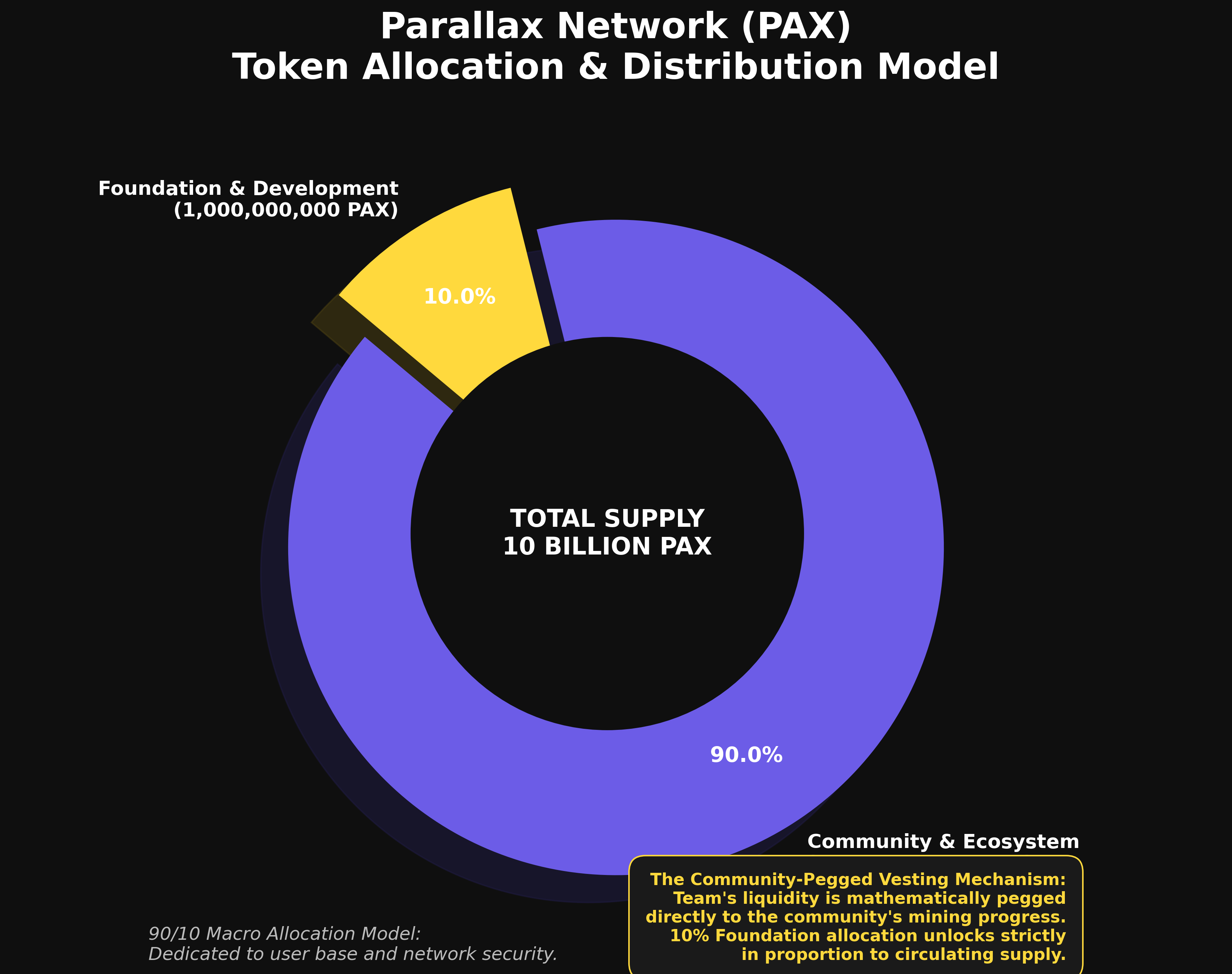
- 90% Community & Ecosystem (9,000,000,000 PAX): Dedicated entirely to the user base. This vast majority encompasses all mobile mining yields, Desktop Validator rewards bonus and network savings.
- 10% Foundation & Development (1,000,000,000 PAX): Allocated to the Parallax Foundation and the core development team. These funds are designated strictly for continuous protocol engineering, global marketing initiatives, promotional campaigns, liquidity and long-term operational maintenance.
The Community-Pegged Vesting Mechanism
A critical vulnerability in traditional Web3 projects is the reliance on time-based team vesting schedules. Time-based unlocks allow founders to access and liquidate tokens based on a calendar date, regardless of whether the network has actually achieved adoption or success.
Parallax eradicates this structural risk by implementing a dynamic release mechanism. The core team's liquidity is mathematically pegged directly to the community's mining progress.
The 10% Foundation allocation does not unlock over time. Instead, it unlocks strictly in proportion to the circulating supply generated by the community. For example: if the community successfully mines 10% of the total network supply (1 Billion PAX), the protocol authorizes the release of exactly 10% of the team's allocated vault (100 Million PAX).
Economic Alignment and Network Security
This architectural decision acts as a permanent security guarantee for the network. It mathematically ensures that the core development team cannot unfairly benefit from their allocated tokens prior to delivering real, tangible growth to the ecosystem. The team is only rewarded when the community expands. This mechanism eliminates internal dump risks, fortifies market stability, and binds the financial success of the founders absolutely to the success and prosperity of the everyday users.
10. The Savings Protocol: Frictionless Yield Generation
Traditional Web3 staking introduces unnecessary friction for the everyday user. Complex smart contract interactions, prolonged unbonding periods, and unpredictable annual yields deter mass adoption. To bridge this gap, Parallax introduces the Savings Protocol. Scheduled for architectural implementation during the Testnet phase and fully activated upon Mainnet launch, this system mirrors the familiar, intuitive mechanics of a traditional bank savings account, yet operates entirely on a decentralized framework.
Yield as a Mining Boost
Unlike conventional staking mechanisms that arbitrarily mint new tokens to pay interest, the Savings Protocol rewards users by amplifying their active participation. The "interest" generated by stored funds is applied directly as a Mining Boost. By allocating tokens to their Savings account, users receive a mathematical multiplier on their ongoing mining yields, aligning passive holding with active network consensus.
Absolute Liquidity and Micro-Locking
The Parallax ecosystem prioritizes user sovereignty. Consequently, the Savings Protocol features zero fixed, long-term lock-up periods. Users are free to unlock and withdraw their funds at any moment.
However, to guarantee network stability during consensus generation, the protocol enforces a Micro-Locking mechanism. If a user initiates a standard 4-hour mining cycle, the funds currently allocated to the Savings Protocol become strictly non-transferable for the exact duration of that cycle. Once the 4-hour cycle concludes, full liquidity and transferability are immediately restored.
The Proportional Boost Calculation
The magnitude of the Mining Boost is determined by the ratio between the user's locked balance and their historically validated (mined) balance. If a user migrates 100 PAX to the Mainnet and chooses to lock 50 PAX in the Savings Protocol, they receive a 50% multiplier on their base mining yield. This directly rewards users who preserve the tokens they organically generated.
The Maturation Phase (Anti-Rotation Safeguard)
To prevent circular liquidity attacks where a single pool of funds is rapidly transferred between multiple accounts to trigger simultaneous mining boosts the Savings Protocol implements a Time-Locked Eligibility mechanism.
While incoming PAX transfers are immediately liquid for standard peer-to-peer transactions or dApp interactions, they are subjected to a Maturation Freeze before they can be allocated to the Savings Protocol. Newly deposited tokens must age organically within the receiving wallet for a minimum designated period (72 hours) before they become eligible to generate a Mining Boost. This mathematical friction ensures that network yield is exclusively distributed to genuine, long-term ecosystem participants, completely neutralizing velocity-based rotational exploits.
The Exponential Decay Safeguard (Anti-Exploit Mechanism)
The protocol permits users to lock liquidity exceeding their originally mined amount. For example, a user who mined 100 PAX can acquire additional tokens on the open market and lock 110 PAX, temporarily achieving a 110% boost.
To protect the network's emission integrity, Parallax implements a strict algorithmic safeguard. The linear boost maxes out when the locked amount matches 100% of the user's natively mined balance. Any locked liquidity that exceeds this 100% threshold triggers an exponential decay curve on the resulting boost. This mathematical friction neutralizes economic exploits, specifically preventing wealthy external actors from purchasing massive token volumes and injecting them into low-activity accounts to drain the network's yield reserves.
11. Conclusion
Parallax Network is not merely a ledger; it is a fundamental redesign of how humans interact with decentralized systems. By stripping away cryptographic friction, implementing mathematically sound tokenomics, and preserving absolute privacy, Parallax is building the infrastructure for the next billion users.
We invite you to participate in this paradigm shift. Not as a spectator. Not merely as an investor. But as a foundational node in a truly usable decentralized world.
Welcome to Parallax Network.